Companies and organisations rely on the d.velop postbox.
Digital Delivery with d.velop postbox
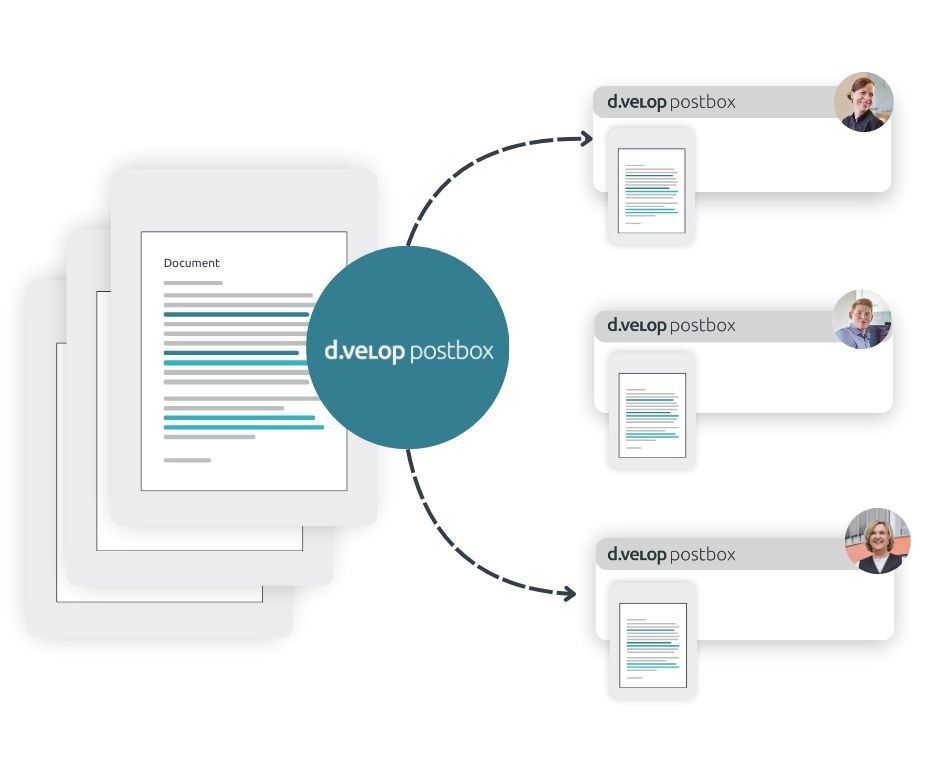
Send documents digitally & securely
Documents such as business letters, invoices or payslips are sensitive records that you need to deliver securely to your customers, partners or employees. And yes – this can be done digitally! With digital delivery via d.velop postbox.
Why? Delivery of documents is encrypted. Documents in d.velop postbox are stored exclusively in Germany: Made in Germany – Safe in Germany. Discover the wide range of features of a digital mailbox for the secure delivery of your business correspondence.
Secure document delivery
Deliver business correspondence digitally and securely to your recipients in a defined folder structure – with just one click. For added security, two-factor authentication is included.

Bulk sending with templates
Create templates for recurring documents such as payslips, contribution notices and more, which can be personalised and delivered to recipients via bulk sending. Recipient assignment is based on predefined rules.
No master data maintenance required
d.velop postbox is a cloud-based solution and owned by the recipients. Each user manages their own data (name, email, address, etc.) independently in their account. This means no additional effort for you in managing recipient accounts or maintaining master data.

Various use cases of d.velop postbox at a glance
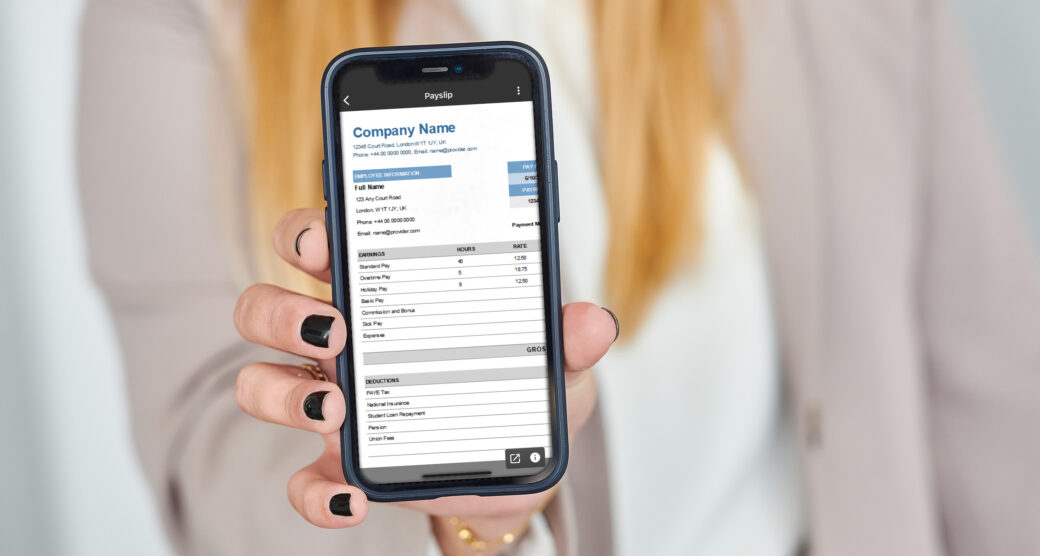
Deliver payslips digitally
With digital payslips, you can reach employees with and without a PC workstation:
- Easily deliver payroll documents digitally
- All employees can access HR documents via the app from anywhere

Deliver IHK contribution notices digitally
IHKs regularly exchange documents with their members. This process should be fully digital:
- Secure and sustainable delivery of contribution notices to members
- Modern, efficient communication with members


Send insurance documents digitally
Insurers need to deliver a wide range of documents – this can also be done digitally and securely:
- Secure delivery to policyholders
- Policyholders can quickly and conveniently upload and share documents

Benefits of Digital Delivery
Advantages of secure, digital delivery
of business mail
Benefits of digital delivery for organisations
- Cost savings by eliminating paper, printing, enveloping, postage and additional manual effort
- Time savings for colleagues, allowing them to focus on efficiency-boosting projects
- No need for costly portal operations or maintenance
- Highest security standards for the entire delivery process and beyond (transport and storage encryption, plus German data centre)
- Hybrid mail: deliver documents digitally or by post to non-digital recipients
- Simple onboarding and seamless integration into existing systems
- Customisation options: web branding, branded email notifications and white-label app
- Audit-proof delivery: once a document is delivered in an audit-proof manner, end users cannot delete it for the specified retention period
Benefits of digital delivery for recipients
- Ownership of documents: The d.velop postbox and all documents delivered to it belong to the recipient, even after leaving the organisation
- One central inbox for documents from multiple senders such as banks, insurers, public authorities and government offices
- Time savings: No need to file paper documents or digitise them later
- d.velop postbox app: Personal documents in one place, always accessible on your smartphone
- Lifetime, free use of the digital mailbox after a one-time registration
- 2 GB storage included for additional personal documents
- Share documents with third parties for easy two-way exchange
- Sustainable office work, reducing CO₂ emissions and paper waste

Digital Delivery White paper
Digital delivery of salary statements and payslips
Read on to learn the key requirements, functions, and advantages of digital mail delivery. Once set up, you’ll soon see how the digital mailbox offers many benefits besides just cost and time savings.
Contents of the White Paper:
- Challenges in HR admin
- Digital payroll definition and process
- Process optimisation
- Technical requirements
- Legal framework
- 5 advantages for HR
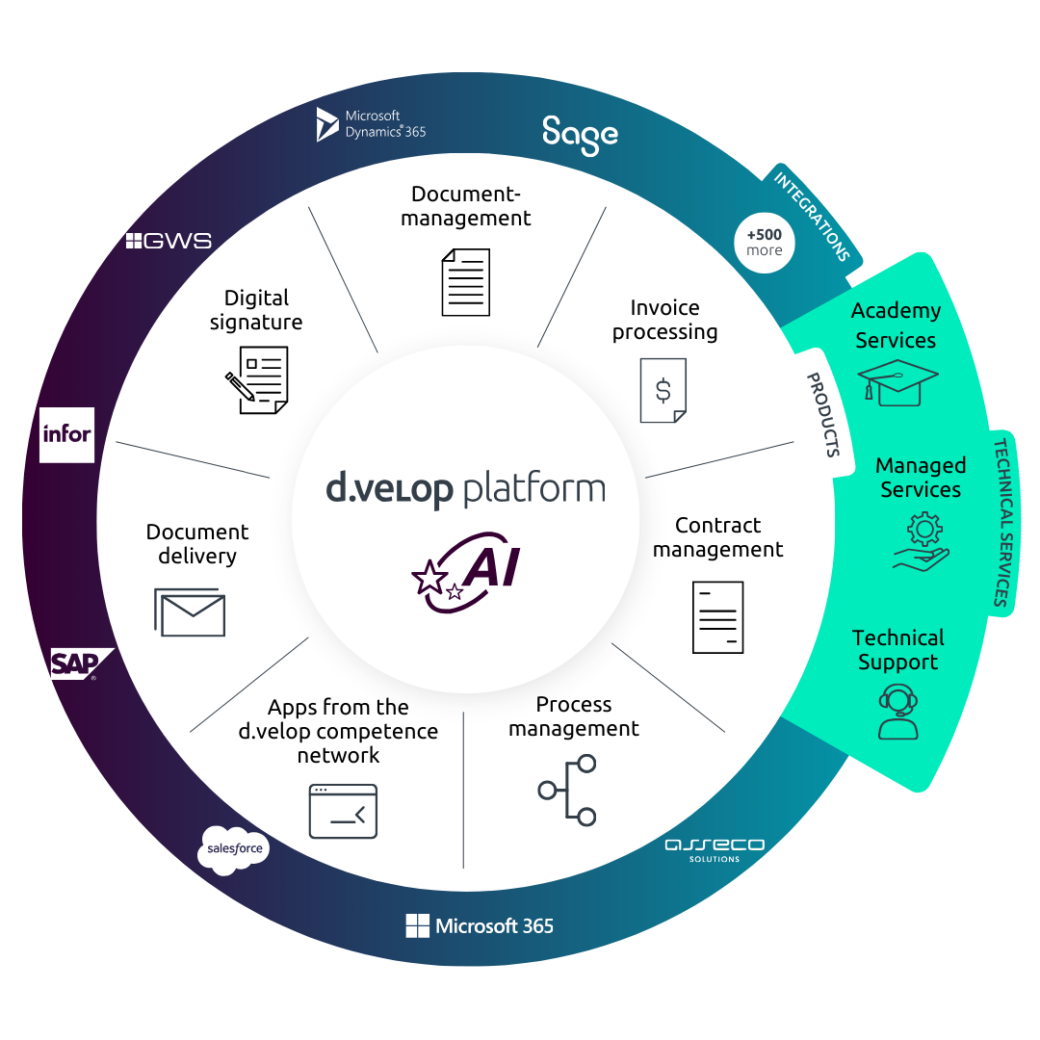
d.velop platform
Unlock the full potential of d.velop.
DMS, ECM, EIM or simply: Connected knowledge
Productive, intelligent, secure: Your d.velop tools.
Digitise, structure, store and make information accessible: our d.velop platform solutions are tailored to your needs, delivering knowledge seamlessly – whether for employees, customers or partners. This not only reduces process costs and saves time, but also eases the workload for your team, creating space for innovative ideas.
News & Resources
Digital delivery explained in detail.
Would you like to learn more about the use of digital delivery? Here you’ll find news and in-depth information.
FAQ
Questions and answers on digital delivery
With d.velop’s digital mail delivery, you can securely deliver, share, and store documents of any kind. The d.velop postbox software solution is excellent for delivering sensitive documents because it operates in compliance with GDPR and follows the highest security standards. Examples of documents that can be sent include employment contracts, salary statements, tax certificates, or social security certificates.
There are numerous benefits of digital mail delivery for your company. With the d.velop postbox solution, you can save costs and time by digitally delivering documents, thus providing long-term relief to your HR department. Through digital and compliant delivery, documents can be delivered in real-time with. Another advantage for your company is that you won’t have any additional effort from tedious master data maintenance since all changes are made by the user. Furthermore, you can leverage the full potential of the d.velop postbox by integrating digital signatures. This allows you to not only deliver documents, but also sign them directly in the d.velop postbox.
Your employees can easily and securely store documents of any kind in the d.velop postbox. When a new document is delivered, your employees receive automatic notifications via email or push notifications if they use the app. Additionally, the d.velop postbox offers great potential beyond the professional context. It can be used privately for free and provides up to 2GB of space for personal documents. Even after the termination of the employment relationship, the d.velop postbox can be used indefinitely to continue accessing the documents.
Let’s take the example of digital salary statements. By digitally delivering salary documents, costs for printing, enveloping, postage, and associated work are eliminated. Let’s focus on printing costs alone: with 500 employees and an average of 6,000 printed pages per year, a total of 5,260€ can be saved annually. When considering all costs, the introduction of digital delivery can save approximately 50 % of the expenses.
The d.velop postbox has been developed according to the highest security standards in Germany and operates under German law. The data center is ISO 27001 and Trustee-Cloud certified. This ensures that every document is encrypted and delivered and stored in compliance with GDPR – using the current industry standard AES-256-bit encryption. For more information on data security, please visit here.
Contact & Consultation
We connect data and people – and look forward to hearing from you.
Curious? We’d be happy to show you our software.
Simply request a live demo.



















